Blog
Insights from experts on Exposure Management, AI security & more

Blog
The GitHub Breach – How it Happened and Actions You Can Take

Blog
What the AI Era Will Change for MedTech Product Security
Blog
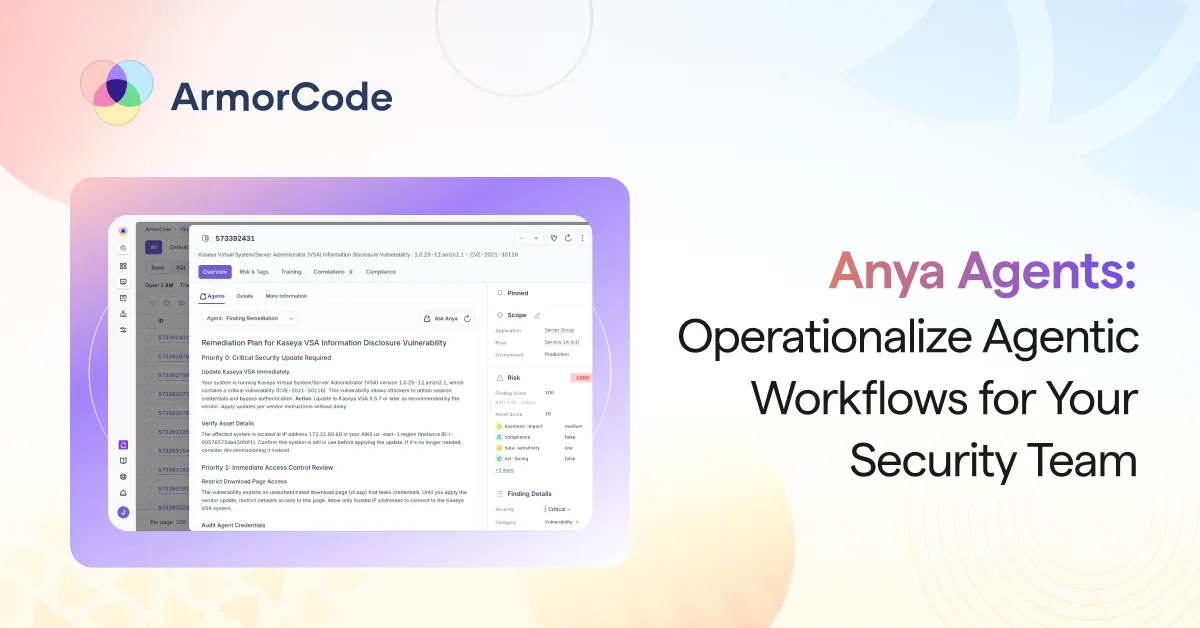
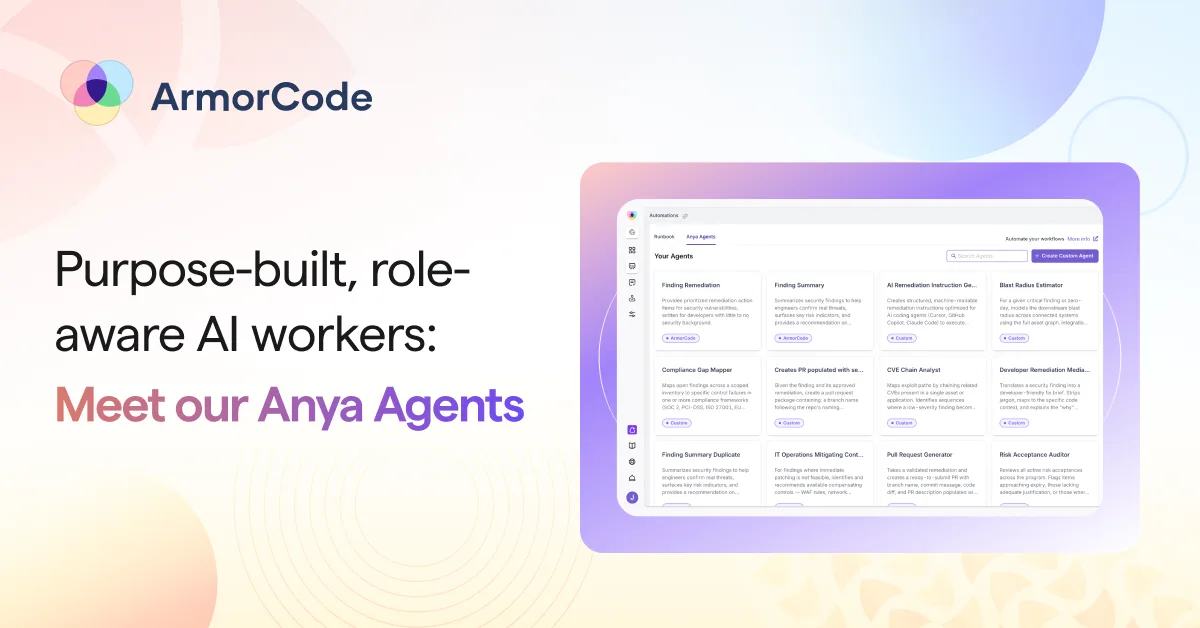
How Anya Agents Operationalize Agentic Workflows for Security Teams

Blog
Evaluating Exposure Management Software: Key Capabilities for 2026
Blog
Agentic Workflows: Introducing Anya Agents for Security

Blog
The Reality Shift in Vulnerability Management

Blog
Mini Shai-Hulud: The NPM Supply Chain Worm Hitting TanStack, Mistral, UiPath, and More
Blog
The Mythos Moment is Real. The Fix-It-Faster Response isn’t.
Blog
The NPM Supply Chain Attack Playbook That Still Works in 2026

Blog
Vulnerability Risk Scoring: Why CVSS Alone Isn’t Enough

Blog
The Unified Exposure Management Solution: Cut Costs, Close More Vulnerabilities

Blog